In today's digitally-driven world, businesses heavily rely on software applications to streamline their operations, enhance customer experiences, and gain a competitive edge. However, building software that is both scalable and secure presents a significant challenge.
Scalability ensures that the software can handle increasing workloads, while security protects against potential threats and vulnerabilities. In this blog, we will explore software development security best practices that businesses can follow to build scalable and secure software.
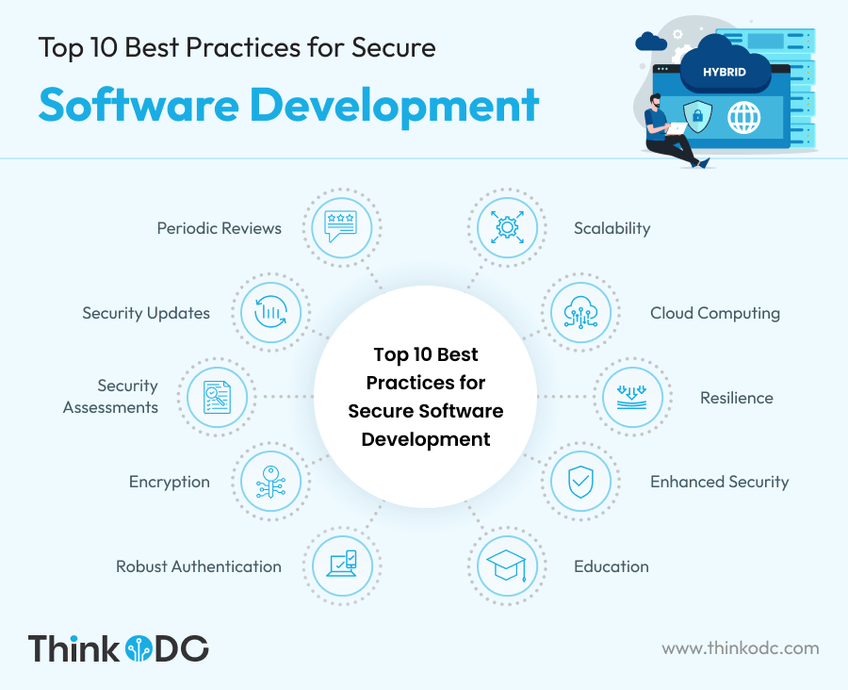
Top 10 Best Practices for Secure Software Development
Whether you are a seasoned software developer or a business owner embarking on a new software development project, our goal is to equip you with the knowledge and tools needed to prioritize security from the outset. From adopting secure coding practices and implementing stringent authentication mechanisms to conducting regular security testing and staying updated with the latest security patches, each step in the development process plays a crucial role in safeguarding your software and its users.
By adhering to these best practices for software development, you can develop a product that meets industry standards, complies with data protection regulations, and most importantly, protects your customers' sensitive data.
Plan for Scalability from the Start
When embarking on a secure software development project, it's crucial to consider scalability right from the planning phase. Define the anticipated growth and ensure the architecture can handle increased user loads, data volumes, and transactions. Employ modular and loosely coupled design principles to enable scalability, allowing individual components to scale independently.
Adopt Cloud Computing
Leveraging cloud computing technologies, such as Infrastructure as a Service (IaaS) and Platform as a Service (PaaS), is a highly effective way to build scalable software. Cloud platforms provide on-demand resources, allowing businesses to easily scale their applications based on user demand. They also offer built-in security features and robust data protection mechanisms, minimizing the risk of unauthorized access.
Design for Resilience and Fault Tolerance
Developing resilient software ensures that it can withstand failures and continue to operate without interruption. Implement redundant systems, load balancing, and failover mechanisms to distribute the workload across multiple servers and minimize downtime. Additionally, use distributed caching techniques and implement error handling and recovery mechanisms to enhance fault tolerance.
Follow Secure Coding Practices
Security must be an integral part of the software development process. Adhere to secure coding practices such as input validation, parameterized queries, and proper error handling to mitigate common vulnerabilities like injection attacks and cross-site scripting. Regularly update libraries and frameworks, apply patches promptly, and conduct thorough security testing and code reviews to identify and address potential security weaknesses.
Educate Your Team
Educate your development team and employees on SDLC best practices. Promote a security-aware culture, and provide training to recognize and respond to security incidents effectively.
Implement Robust Authentication and Authorization
Establishing strong authentication and authorization mechanisms is vital to safeguarding software applications. Utilize secure authentication protocols like OAuth or OpenID Connect and employ strong password policies, multi-factor authentication, and session management techniques. Implement role-based access control (RBAC) to ensure that users have appropriate permissions based on their roles and responsibilities.
Encrypt Sensitive Data
Protecting sensitive data should be a top priority. Encrypt data at rest and in transit using industry-standard encryption algorithms. Implement secure key management practices and avoid hard-coding sensitive information within the application's source code. Utilize secure protocols such as HTTPS for communication and regularly audit encryption mechanisms to identify and address potential vulnerabilities.
Conduct Regular Security Assessments
Performing regular security assessments, including penetration testing and vulnerability scanning, is crucial to identify potential weaknesses in software applications. Engage security experts to perform comprehensive assessments and identify vulnerabilities that may be missed during the development process. Conducting periodic security audits helps ensure that the software remains secure as new threats emerge. You can check and assess the aspects of software to secure web application development.
Keep Abreast of Security Updates and Threat Landscape
Stay informed about the latest security updates, patches, and vulnerabilities related to the software components and libraries being used. Establish a process to promptly apply security updates and patches. Monitor industry news and subscribe to security bulletins to stay up to date with emerging threats and vulnerabilities, allowing you to proactively address any potential risks.
Regular Security Reviews
After the software is deployed, conduct regular security reviews and assessments to identify and address any new security risks or changes in the threat landscape. By conducting periodic security reviews, you can assess the effectiveness of your existing security measures, identify any emerging threats, and implement necessary updates or patches promptly.
Furthermore, keep your development team well-informed about the latest security trends and best practices. Encourage continuous learning and professional development to ensure they stay up-to-date with the ever-changing security landscape. Implementing a culture of vigilance and proactive security measures will instill confidence in your customers and stakeholders, demonstrating your commitment to protecting their data and privacy.
How to develop secure and scalable software?
Building scalable and secure software is essential for businesses to thrive in today's technology-driven landscape. By following these SDLC best practices, organizations can create software applications that can handle increasing workloads while providing robust protection against potential security threats. Prioritizing scalability and security from the early stages of software development not only ensures a better user experience but also instills trust among customers and stakeholders, contributing to the long-term success of the business.
Regular security assessments and staying updated on security updates and the evolving threat landscape are equally important. By conducting thorough assessments and promptly addressing vulnerabilities, businesses can proactively mitigate risks and keep their software applications secure.
It's important to note that building scalable and secure software is an ongoing effort. As technology evolves, so do threats and vulnerabilities. Businesses must remain vigilant, adapt to new challenges, and continuously improve their software's scalability and security measures.
By prioritizing scalability and security throughout the software development lifecycle, businesses can gain a competitive advantage, provide a seamless user experience, and safeguard critical data. Embracing these best practices ensures that businesses are well-prepared to meet the demands of a rapidly changing digital landscape while maintaining the trust and confidence of their customers and stakeholders.
Scalable and secure software development requires a collaborative effort from various stakeholders, including security software developers, architects, security professionals, and business leaders. It involves staying up to date with the latest security practices, emerging threats, and technological advancements. Continuous monitoring, testing, and improvement are essential to address vulnerabilities and adapt to the evolving security landscape.
Conclusion
Ultimately, investing in scalable and secure software development practices is an investment in the future success and resilience of a business. It sets the foundation for innovation, growth, and customer satisfaction. By adhering to best practices and making scalability and security integral to the software development process, businesses can confidently navigate the digital landscape, meet user expectations, and safeguard their valuable assets. We, at ThinkODC, a reliable software development company, offer exceptional results to the clients worldwide.


